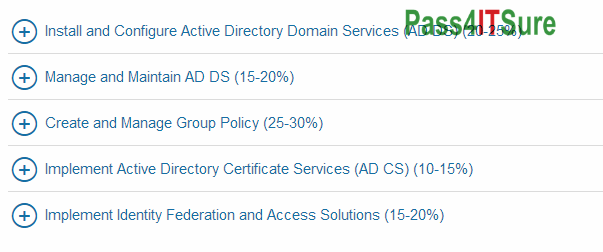
Who can share new Microsoft 70-742 dumps? The Identity with Windows Server 2016 (70-742 Windows Server) exam is a 97 questions assessment in pass4itsure that is associated with the MCSA certification. Welcome to buy 100% guarantee Microsoft 70-742 dumps Windows Server exam materials Identity with Windows Server 2016 Youtube online free share. “Identity with Windows Server 2016” is the exam name of Pass4itsure Microsoft 70-742 dumps test which designed to help candidates prepare for and pass the Microsoft 70-742 exam. You can use our samples first to experience the effect of our software, and we believe that you can realize our profession and efforts by researching and developing Microsoft https://www.pass4itsure.com/70-742.html dumps materials exam software from samples of Microsoft 70-742 dumps materials.
[Ensure Pass4itsure 70-742 Dumps Exam From Google Drive]: https://drive.google.com/open?id=0BwxjZr-ZDwwWZDZVWjB6Wno5dzg
[Ensure Pass4itsure 1Y0-371 Dumps Exam From Google Drive]: https://drive.google.com/open?id=0BwxjZr-ZDwwWekxPNnBJU1N6WWc
Latest and Most Accurate Pass4itsure 70-742 Dumps Exam Q&As(1-16)
QUESTION 1
What is the essential difference between an `Ethical Hacker’ and a `Cracker’?
A. The ethical hacker does not use the same techniques or skills as a cracker.
B. The ethical hacker does it strictly for financial motives unlike a cracker.
C. The ethical hacker has authorization from the owner of the target.
D. The ethical hacker is just a cracker who is getting paid.
70-742 exam Correct Answer: C
Explanation
Explanation/Reference:
Explanation:
The ethical hacker uses the same techniques and skills as a cracker and the motive is to find the security breaches before a cracker does. There is nothing that says that a cracker does not get paid for the work he does, a ethical hacker has the owners authorization and will get paid even if he does not succeed to penetrate the target.
QUESTION 2
What does the term “Ethical Hacking” mean?
A. Someone who is hacking for ethical reasons.
B. Someone who is using his/her skills for ethical reasons.
C. Someone who is using his/her skills for defensive purposes.
D. Someone who is using his/her skills for offensive purposes.
Correct Answer: C
Explanation
Explanation/Reference:
Explanation:
Ethical hacking is only about defending your self or your employer against malicious persons by using the same techniques and skills.
QUESTION 3
Who is an Ethical Hacker?
A. A person who hacks for ethical reasons
B. A person who hacks for an ethical cause
C. A person who hacks for defensive purposes
D. A person who hacks for offensive purposes
70-742 dumps Correct Answer: C
Explanation
Explanation/Reference:
Explanation:
The Ethical hacker is a security professional who applies his hacking skills for defensive purposes.
QUESTION 4
What is “Hacktivism”?
A. Hacking for a cause
B. Hacking ruthlessly
C. An association which groups activists
D. None of the above
Correct Answer: A
Explanation
Explanation/Reference:
Explanation:
The term was coined by author/critic Jason Logan King Sack in an article about media artist Shu Lea Cheang. Acts of hacktivism are carried out in the belief that proper use of code will have leveraged effects similar to regular activism or civil disobedience.
QUESTION 5
Where should a security tester be looking for information that could be used by an attacker against an organization? (Select all that apply)
A. CHAT rooms
B. WHOIS database
C. News groups
D. Web sites
E. Search engines
F. Organization’s own web site
70-742 pdf Correct Answer: ABCDEF
Explanation
Explanation/Reference:
Explanation:
A Security tester should search for information everywhere that he/she can access. You never know where you find that small piece of information that could penetrate a strong defense.
QUESTION 6
What are the two basic types of attacks?Choose two.
A. DoS
B. Passive
C. Sniffing
D. Active
E. Cracking
Correct Answer: BD
Explanation
Explanation/Reference:
Explanation:
Passive and active attacks are the two basic types of attacks.
QUESTION 7
The United Kingdom (UK) he passed a law that makes hacking into an unauthorized network a felony.
The law states:
Section1 of the Act refers to unauthorized access to computer material. This states that a person commits an offence if he causes a computer to perform any function with intent to secure unauthorized access to any program or data held in any computer. For a successful conviction under this part of the Act, the prosecution must prove that the access secured is unauthorized and that the suspect knew that this was the case. This section is designed to deal with common or-graden hacking. Section 2 of the deals with unauthorized access with intent to commit or facilitate the commission of further offences. An offence is committed under Section 2 if a Section 1 offence has been committed and there is the intention of committing or facilitating a further offense (any offence which attacks a custodial sentence of more than five years, not necessarily one covered but the Act). Even if it is not possible to prove the intent to commit the further offence, the Section 1 offence is still committed. Section 3 Offences cover unauthorized modification of computer material, which generally means the creation and distribution of viruses. For conviction to succeed there must have been the intent to cause the modifications and knowledge that the modification had not been authorized
What is the law called?
A. Computer Misuse Act 1990
B. Computer incident Act 2000
C. Cyber Crime Law Act 2003
D. Cyber Space Crime Act 1995
70-742 vce Correct Answer: A
Explanation
Explanation/Reference:
Explanation:
Computer Misuse Act (1990) creates three criminal offences:
QUESTION 8
Which of the following best describes Vulnerability?
A. The loss potential of a threat
B. An action or event that might prejudice security
C. An agent that could take advantage of a weakness
D. A weakness or error that can lead to compromise
Correct Answer: D
Explanation
Explanation/Reference:
Explanation:
A vulnerability is a flaw or weakness in system security procedures, design or implementation that could be exercised (accidentally triggered or intentionally exploited) and result in a harm to an IT system or activity.
QUESTION 9
Steven works as a security consultant and frequently performs penetration tests for Fortune 500 companies. Steven runs external and internal tests and then creates reports to show the companies where their weak areas are. Steven always signs a non-disclosure agreement before performing his tests. What would Steven be considered?
A. Whitehat Hacker
B. BlackHat Hacker
C. Grayhat Hacker
D. Bluehat Hacker
70-742 exam Correct Answer: A
Explanation
Explanation/Reference:
Explanation:
A white hat hacker, also rendered as ethical hacker, is, in the realm of information technology, a person who is ethically opposed to the abuse of computer systems. Realization that the Internet now represents human voices from around the world has made the defense of its integrity an important pastime for many. A white hat generally focuses on securing IT systems, whereas a black hat (the opposite) would like to break into them.
QUESTION 10
Which of the following act in the united states specifically criminalizes the transmission of unsolicited commercial e mail(SPAM) without an existing business relationship.
A. 2004 CANSPAM Act
B. 2003 SPAM Preventing Act
C. 2005 US-SPAM 1030 Act
D. 1990 Computer Misuse Act
Correct Answer: A
Explanation
Explanation/Reference:
Explanation:
The CAN-SPAM Act of 2003 (Controlling the Assault of Non-Solicited Pornography and Marketing Act) establishes requirements for those who send commercial email, spells out penalties for spammers and companies whose products are advertised in spam if they violate the law, and gives consumers the right to ask emailers to stop spamming them. The law, which became effective January 1, 2004, covers email whose primary purpose is advertising or promoting a commercial product or service, including content on a Web site. A “transactional or relationship message” email that facilitates an agreed-upon transaction or updates a customer in an existing business relationship may not contain false or misleading routing information, but otherwise is exempt from most provisions of the CAN-SPAM Act.
QUESTION 11
ABC.com is legally liable for the content of email that is sent from its systems, regardless of whether the message was sent for private or business-related purpose. This could lead to prosecution for the sender and for the company’s directors if, for example, outgoing email was found to contain material that was pornographic, racist or likely to incite someone to commit an act of terrorism. You can always defend yourself by “ignorance of the law” clause.
A. True
B. False
70-742 dumps Correct Answer: B
Explanation
Explanation/Reference:
Explanation:
Ignorantia juris non excusat or Ignorantia legis neminem excusat (Latin for “ignorance of the law does not excuse” or “ignorance of the law excuses no one”) is a public policy holding that a person who is unaware of a law may not escape liability for violating that law merely because he or she was unaware of its content; that is, persons have presumed knowledge of the law. Presumed knowledge of the law is the principle in jurisprudence that one is bound by a law even if one does not know of it. It has also been defined as the “prohibition of ignorance of the law”.
QUESTION 12
You are footprinting Acme.com to gather competitive intelligence. You visit the acme.com websire for contact information and telephone number numbers but do not find it listed there. You know that they had the entire staff directory listed on their website 12 months ago but now it is not there. How would it be possible for you to retrieve information from the website that is outdated?
A. Visit google search engine and view the cached copy.
B. Visit Archive.org site to retrieve the Internet archive of the acme website.
C. Crawl the entire website and store them into your computer.
D. Visit the company’s partners and customers website for this information.
Correct Answer: B
Explanation
Explanation/Reference:
Explanation:
The Internet Archive (IA) is a non-profit organization dedicated to maintaining an archive of Web and multimedia resources. Located at the Presidio in San Francisco, California, this archive includes “snapshots of the World Wide Web” (archived copies of pages, taken at various points in time), software, movies, books, and audio recordings (including recordings of live concerts from bands that allow it). This site is found at www.archive.org.
QUESTION 13
User which Federal Statutes does FBI investigate for computer crimes involving e-mail scams and mail fraud?
A. 18 U.S.C 1029 Possession of Access Devices
B. 18 U.S.C 1030 Fraud and related activity in connection with computers
C. 18 U.S.C 1343 Fraud by wire, radio or television
D. 18 U.S.C 1361 Injury to Government Property
E. 18 U.S.C 1362 Government communication systems
F. 18 U.S.C 1831 Economic Espionage Act
G. 18 U.S.C 1832 Trade Secrets Act
70-742 pdf Correct Answer: B
Explanation
Explanation/Reference:
Explanation:
QUESTION 14
Which of the following activities will NOT be considered as passive footprinting?
A. Go through the rubbish to find out any information that might have been discarded.
B. Search on financial site such as Yahoo Financial to identify assets.
C. Scan the range of IP address found in the target DNS database.
D. Perform multiples queries using a search engine.
Correct Answer: C
Explanation
Explanation/Reference:
Explanation:
Passive footprinting is a method in which the attacker never makes contact with the target systems. Scanning the range of IP addresses found in the target DNS is considered making contact to the systems behind the IP addresses that is targeted by the scan.
QUESTION 15
Which one of the following is defined as the process of distributing incorrect Internet Protocol (IP) addresses/names with the intent of diverting traffic?
A. Network aliasing
B. Domain Name Server (DNS) poisoning
C. Reverse Address Resolution Protocol (ARP)
D. Port scanning
70-742 vce Correct Answer: B
Explanation
Explanation/Reference:
Explanation:
This reference is close to the one listed DNS poisoning is the correct answer. This is how DNS DOS attack can occur. If the actual DNS records are unattainable to the attacker for him to alter in this fashion, which they should be, the attacker can insert this data into the cache of there server instead of replacing the actual records, which is referred to as cache poisoning.
QUESTION 16
You are footprinting an organization to gather competitive intelligence. You visit the company’s website for contact information and telephone numbers but do not find it listed there. You know that they had the entire staff directory listed on their website 12 months ago but not it is not there. How would it be possible for you to retrieve information from the website that is outdated?
A. Visit google’s search engine and view the cached copy.
B. Visit Archive.org web site to retrieve the Internet archive of the company’s website.
C. Crawl the entire website and store them into your computer.
D. Visit the company’s partners and customers website for this information.
Correct Answer: B
Explanation
Explanation/Reference:
It is very normal to be afraid of the exam, especially such difficult exam like Microsoft 70-742 dumps exam. We know that encouragement alone cannot really improve your confidence in exam, so we provide the most practical and effective test software to help you pass the Microsoft 70-742 dumps exam. “Identity with Windows Server 2016”, also known as 70-742 exam, is a Microsoft certification which covers all the knowledge points of the real Microsoft exam. Pass4itsure Microsoft 70-742 dumps exam questions answers are updated (97 Q&As) are verified by experts. The associated certifications of https://www.pass4itsure.com/70-742.html dumps is MCSA.